Too Many Tools? Tech Overload is Emerging as a Hidden Threat to SME Productivity

SMEs and digital transformation: From promise to platform fatigue
UK SMEs are embracing digital tools at speed, but fragmented adoption is creating inefficiencies and frustration. Discover why a strategic approach to integration is essential for sustainable growth.
Digital transformation has become a defining priority for UK small and medium-sized enterprises (SMEs). From project management platforms and communication apps to finance and HR software, the digital toolkit of the average SME has expanded rapidly. This surge in adoption reflects a desire to remain competitive, improve collaboration and unlock new growth opportunities in an increasingly digital economy.
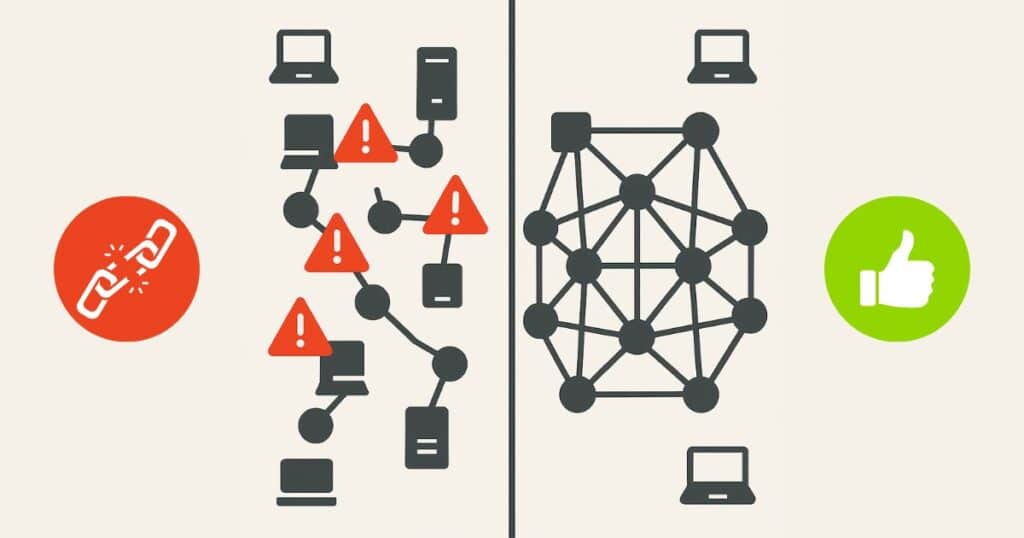
However, the SME Digital Adoption Task Force’s final report reveals a critical challenge: while adoption is high, strategic integration is often missing. Many businesses invest in multiple tools to meet immediate needs without a cohesive plan for how these platforms will work together. The result is a fragmented ecosystem that creates friction, slows decision-making and undermines productivity.
This episode explores the concept of “platform fatigue” – the strain caused by juggling multiple systems with different interfaces, logins and workflows. Employees waste time switching between tools, duplicating work and troubleshooting compatibility issues. Information becomes siloed and the cognitive load of managing disjointed platforms leads to frustration and disengagement. Beyond the human impact, the financial cost is significant. Subscription fees for overlapping tools and underused features quietly erode budgets, making it harder for SMEs to invest in innovation.
The discussion highlights practical steps to overcome these challenges. Rather than reacting to short-term needs, SMEs should adopt a strategic approach to digital investment. This means prioritising usability, integration and alignment with existing workflows. Tools should be chosen for their ability to deliver real value, not just for their features. Training and standardised processes are essential to ensure adoption is smooth and effective.
Government and industry support also play a role, with calls for improved digital literacy programmes and resources to help SMEs make informed decisions. Ultimately, the goal is not to use more technology, but to use the right technology intelligently and intentionally. By simplifying digital environments and reducing complexity, businesses can boost efficiency, improve morale and create a foundation for sustainable growth.
You may be interested in
Zero Trust Networking
Protecting Employees Without Friction Your workforce is your greatest asset, and your greatest vulnerability. Attackers know this, which is why phishing and credential theft remain the most common entry points. But here’s the leadership challenge: how do you protect employees without slowing them down? Zero Trust answers that question by making security invisible yet uncompromising. Employees work from anywhere, home, client sites, airports, without clunky VPNs or endless password resets. Behind the scenes, every login is verified, every device assessed, every anomaly flagged. If something looks wrong, a compromised credential, an unusual location, the system reacts…
Shadow AI: Executive Briefing on Real Risks, Business Impact and Mitigation
Shadow AI is here, and it’s growing Shadow AI is the use of artificial intelligence tools and platforms outside the oversight of IT, security, or compliance teams. This is not a hypothetical concern. KPMG’s 2025 global survey found that up to 58% of employees are using AI productivity tools daily, and nearly half admit to uploading sensitive company information to unauthorised platforms. Only 41% of employees say their organisation has a policy guiding the use of generative AI, revealing a significant governance gap. The Risks Are Real and Substantial The evidence from leading analysts and recent incidents is clear:…
Cyber Resilience in 2025: From Tick-Box to Boardroom Imperative
What the NCSC’s 2025 Review Means for UK Businesses The National Cyber Security Centre’s (NCSC) 2025 Annual Review is a wake-up call for business leaders across the UK. The days when cyber security was simply an IT concern or a routine compliance task are over. With a record number of nationally significant cyber incidents handled in the past year (more than double the previous year’s figure), it is clear that cyber risks have become a central issue for organisational survival and national prosperity. The Evolving Threat: Why Businesses Can’t Afford Complacency No sector has been spared in the latest…
AI and supply chain threats to shape cybersecurity risks for UK businesses in 2026, warns Espria
Five major cybersecurity trends will dominate 2026, signalling the need for real-time, intelligence-driven protection. Smarter, faster and more interconnected cyber threats will reshape the UK risk landscape in 2026, with traditional security models no longer able to keep pace, according to new analysis from Espria. Brian Sibley, Virtual CTO at Espria warns that organisations are entering a cybersecurity environment defined by AI-driven attacks, opaque supply chains, expanding digital ecosystems and rising insurance scrutiny. Yet many businesses still rely on fragmented tools, manual processes or outdated perimeter defences that cannot withstand the speed and sophistication of emerging threats. “Threat actors are innovating faster than ever. AI has changed the economics of attack; the…
Building a security-first framework against evolving cyberthreats
Written by Brian Sibley, Virtual CTO at Espria As the UK’s network and cloud security market evolves at an unprecedented pace, businesses face a barrage of sophisticated cyber threats and tightening regulations. Connectivity across business infrastructure has created an enormous attack surface for organisations of all sizes, meaning that cyber risk is undoubtedly a business risk at every level. The era of selling security products as an add-on is over; managed service providers must now redefine their role from purely IT consultants and suppliers of managed services to indispensable security partners, delivering true, measurable cyber…
When IT operates in silos, businesses pay the price
The recent European airports cyberattack illustrates the systemic danger of siloed IT systems for organisations of all sizes. Businesses are investing more in digital technology than ever before, yet many are managing their IT services as disconnected pieces rather than as a single integrated entity. Connectivity, cloud, communications, print and security are often handled by separate providers, creating hidden inefficiencies and increasing exposure to risk. The recent cyberattack that disabled check-in systems at major European airports, including Heathrow, Brussels and Berlin, offers a stark illustration of the consequences when critical IT systems operate in silos. “The airport incident is a wake-up call for every business,” said Brian…