The State of Ransomware – An overview of Sophos’ 2025 Report

In the first of 3 episodes covering Sophos’ 2025 report ‘The State of Ransomware’, Brian Sibley, VCTO at Espria and Jon Hope, Cyber Security Evangelist at Sophos discuss the findings of this year’s report, and specifically its implications for the UK.
In this episode the team will reveal key findings that cover the scale and impact of ransomware in the UK, including 70% of attacks resulted in data being encrypted and 26% of encryption-led attacks also involved data theft. The team also discuss the report in comparison to the findings of the 2024 report, the trends and shifts in attack tactics and their outcomes. Gain an understanding of the real-world implications for UK businesses across various sizes and sectors.
This podcast episode delves into the complexities of ransomware attacks, highlighting both technological and human factors that contribute to their success. It underscores the importance of a multi-layered defence strategy combining technology, human expertise and education.
Brian and Jon discuss how ransomware attacks are frequently caused by multiple factors, including both technology vulnerabilities and human errors. Exploited software vulnerabilities are the most common cause, accounting for about 32% of successful attacks. These vulnerabilities are usually flaws in software that cybercriminals exploit to execute malicious code. Whereas remote ransomware attacks involve cybercriminals using vulnerable or unmanaged devices within a network to attack other devices that store valuable data. Traditional endpoint protection often fails to detect these lateral attacks.
Human factors also play a significant role in ransomware infiltration. Compromised user credentials, often obtained through social engineering tactics such as phishing, are a common cause. Phishing remains a significant threat vector, relying on human interaction to succeed. Cybercriminals craft highly convincing emails using AI to mimic brand language, tone and logos, making it difficult for users to distinguish legitimate messages from malicious ones.
Organisations face operational challenges such as a lack of skilled cybersecurity personnel, insufficient time to dedicate to security and acceptance of certain security gaps as risks. These challenges underscore the need for adequate resources and comprehensive security strategies.
The podcast emphasises the importance of security data and logs as critical defence tools. Extended Detection and Response (XDR) platforms consolidate security data into a single location for easier analysis. Managed Detection and Response (MDR) services provide 24/7 expert monitoring and analysis, offering a cost-effective alternative to building an in-house team. Integrating data from various tools allows for comprehensive visibility and early warnings.
Backups are crucial for recovery, but cybercriminals often target them first. Integrations with backup vendors can enable monitoring for suspicious changes. The discussion concludes by emphasising that while recovery capabilities are improving, preventing ransomware attacks remains the priority. Early detection through human-led threat hunting, combined with integrated technology tools, and continuous education are key to defending against sophisticated ransomware threats.
You may be interested in
Zero Trust Networking
Protecting Employees Without Friction Your workforce is your greatest asset, and your greatest vulnerability. Attackers know this, which is why phishing and credential theft remain the most common entry points. But here’s the leadership challenge: how do you protect employees without slowing them down? Zero Trust answers that question by making security invisible yet uncompromising. Employees work from anywhere, home, client sites, airports, without clunky VPNs or endless password resets. Behind the scenes, every login is verified, every device assessed, every anomaly flagged. If something looks wrong, a compromised credential, an unusual location, the system reacts…
Shadow AI: Executive Briefing on Real Risks, Business Impact and Mitigation
Shadow AI is here, and it’s growing Shadow AI is the use of artificial intelligence tools and platforms outside the oversight of IT, security, or compliance teams. This is not a hypothetical concern. KPMG’s 2025 global survey found that up to 58% of employees are using AI productivity tools daily, and nearly half admit to uploading sensitive company information to unauthorised platforms. Only 41% of employees say their organisation has a policy guiding the use of generative AI, revealing a significant governance gap. The Risks Are Real and Substantial The evidence from leading analysts and recent incidents is clear:…
Cyber Resilience in 2025: From Tick-Box to Boardroom Imperative
What the NCSC’s 2025 Review Means for UK Businesses The National Cyber Security Centre’s (NCSC) 2025 Annual Review is a wake-up call for business leaders across the UK. The days when cyber security was simply an IT concern or a routine compliance task are over. With a record number of nationally significant cyber incidents handled in the past year (more than double the previous year’s figure), it is clear that cyber risks have become a central issue for organisational survival and national prosperity. The Evolving Threat: Why Businesses Can’t Afford Complacency No sector has been spared in the latest…
AI and supply chain threats to shape cybersecurity risks for UK businesses in 2026, warns Espria
Five major cybersecurity trends will dominate 2026, signalling the need for real-time, intelligence-driven protection. Smarter, faster and more interconnected cyber threats will reshape the UK risk landscape in 2026, with traditional security models no longer able to keep pace, according to new analysis from Espria. Brian Sibley, Virtual CTO at Espria warns that organisations are entering a cybersecurity environment defined by AI-driven attacks, opaque supply chains, expanding digital ecosystems and rising insurance scrutiny. Yet many businesses still rely on fragmented tools, manual processes or outdated perimeter defences that cannot withstand the speed and sophistication of emerging threats. “Threat actors are innovating faster than ever. AI has changed the economics of attack; the…
Building a security-first framework against evolving cyberthreats
Written by Brian Sibley, Virtual CTO at Espria As the UK’s network and cloud security market evolves at an unprecedented pace, businesses face a barrage of sophisticated cyber threats and tightening regulations. Connectivity across business infrastructure has created an enormous attack surface for organisations of all sizes, meaning that cyber risk is undoubtedly a business risk at every level. The era of selling security products as an add-on is over; managed service providers must now redefine their role from purely IT consultants and suppliers of managed services to indispensable security partners, delivering true, measurable cyber…
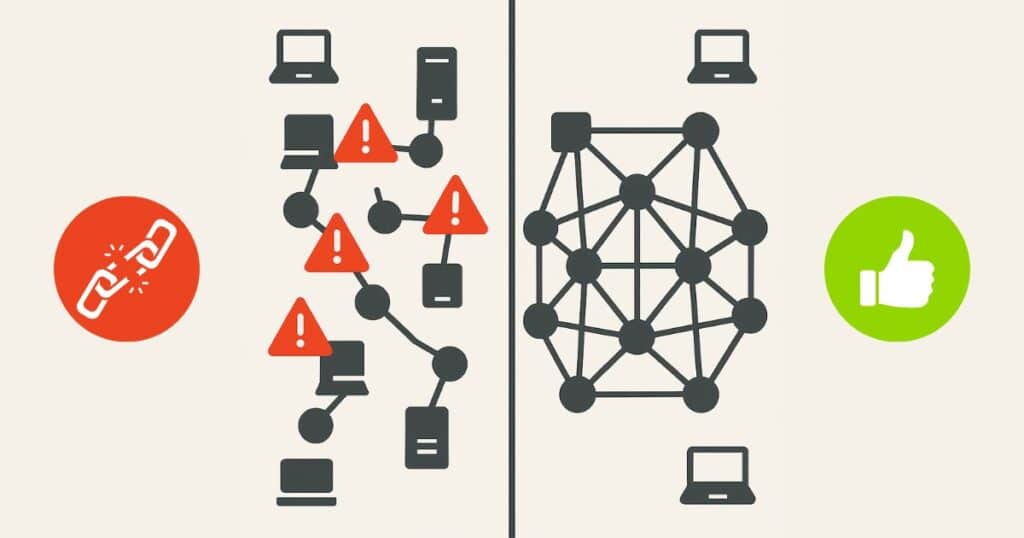
When IT operates in silos, businesses pay the price
The recent European airports cyberattack illustrates the systemic danger of siloed IT systems for organisations of all sizes. Businesses are investing more in digital technology than ever before, yet many are managing their IT services as disconnected pieces rather than as a single integrated entity. Connectivity, cloud, communications, print and security are often handled by separate providers, creating hidden inefficiencies and increasing exposure to risk. The recent cyberattack that disabled check-in systems at major European airports, including Heathrow, Brussels and Berlin, offers a stark illustration of the consequences when critical IT systems operate in silos. “The airport incident is a wake-up call for every business,” said Brian…